What You Need
- Livekd Could Not Resolve Symbols For Ntoskrnl.exe 8
- Livekd Could Not Resolve Symbols For Ntoskrnl.exe 7
- Livekd Could Not Resolve Symbols For Ntoskrnl.exe 11
. ERROR: Module load completed but symbols could not be loaded for ntoskrnl.exe Loading Kernel Symbols Press ctrl-c (cdb, kd, ntsd) or ctrl-break (windbg) to abort symbol loads that take too long. Resolve Symbols; Yes,livekd.exe opened up the kd.exe,but after this, it loaded c: windows system32 livekd.dmp, I checked the file is 0kb. Then it loaded symbols,looks the kernel symbols is ok, load the user symbols. I installed retail symbols in D. Downloaded symbol files for WinDbg.exe do not load. ERROR: Symbol file could not be found.
- The Windows Server 2008 VM handed out by your instructor.This project can be done on other machines, including Windows 10, butfirst you'll need toinstall Windbg and LiveKD
Purpose
Practice using simple WinDbg commands.We'll useLiveKd, a utility that makes some limited kerneldebugging possible with a single computer. LiveKdis read-only -- you can look atkernel processes and data structures, butcannot modify a running system or use breakpoints.Using LiveKd
In a Command Prompt window, execute this command:When Livekd starts, it asks youwhether to set the _NT_SYMBOL_PATHautomatically, as shown below.Type y and press Enter.
Livekd asks 'Enter the folder to which symbols download'. Press Enter to accept the default option.
Windbg launches, as shown below.
This is a strange combination of a GUI andcommand-line, like the other debuggers we've used.Commands are typed into the box at the bottom and the resultsappear in the large top pane.
At the bottom of the Command window,in the command bar, execute this command:
You should see the 'kd> !process' command,and its output, showing informationabout the windbg process, includingits Cid number,as shown below.When I did it, the Cid was 0b14 in hexadecimal,which is 11*256 + 16 + 4 = 2836.
Viewing Processes with Task Manager
At the bottom of the desktop, point to an unused portionof the taskbar and right-click. Click'Task Manager'. In Task Manager, clickthe Processes tab.Find the windbg process, and its PID,as shown below. It should match the Cid fromWindbg.
Close Task Manager.In Windbg,at the bottom of the Command window,in the command bar, execute this command:
You see a long list of all processes,as shown below.Online Help
At the bottom of the Command window,in the command bar, execute this command:You see a brief help message about the'process' command,as shown below.At the bottom of the Command window,in the command bar, execute this command:
You see a much more complete helpwindow,as shown below.Livekd Could Not Resolve Symbols For Ntoskrnl.exe 8
Listing Modules with lm
At the bottom of the Command window,in the command bar, execute this command:A long list of all loaded modules scrollsby.Scroll back to see the lmcommand you entered, and the first fewloaded kernel modules, as shown below.
Scroll down to find the module namednt, as shown below.It's easy to spot because it'e one of thefew modules that shows a Symbols path.
This is Ntoskrnl, the main kernelmodule.
Viewing Memory
Here are some commands that display memory:ddDisplay dwords (32-bit values)daDisplay ASCII textdbDisplay Bytes and ASCII textdtDisplay Type: Information about a variable, data type, or structure
dd nt
You see the first several bytes ofNtoskrnl.exe, as shown below.
This may be more familiar inASCII.
In WinDbg, execute this command:
da nt
You see the characters 'MZ' --theyare at the start of every EXE file.
In WinDbg, execute this command:
db nt
This displays the bytes on the left,and the ASCII on the right.Now you can see the message'This program cannotbe run in DOS mode',which appears at the startof many EXE files.
Examining Symbols
The x command examinessymbols, which include function names.Searching for Functions
In WinDbg, execute this command:x nt!*
This finds all the functions in Ntoskrnl.There are a lot of them,as shown below. It may take a minuteor so to show them.
In WinDbg, execute this command:
x nt!*Create*
This finds all the symbols in Ntoskrnlthat contain the word 'Create'.
There are a lot of them, too.
In WinDbg, execute this command:
x nt!*CreateFile*
Killing floor 'london's finest character pack for macbook pro. This finds all the symbols in Ntoskrnlthat contain the word 'CreateFile'.
There are only about ten of those,including 'nt!NtCreateFile',as shown below:
Unassembling a Function
In WinDbg, execute this command:u nt!NtCreateFile
This shows the first few bytes of thefunction, disassembled,as shown below:
To see more of this function,it helps to use theWinDbg Disassembly window.
If the Command window is maximized,make it smaller.
From the WinDbg menu bar, clickView, Disassembly,as shown below:
In the Offset bar at the top,enter
nt!NtCreateFile
This shows the assembly code beforeand after the start of the NtCreateFilefunction. Using the up-arrowand down-arrow keys, you canscroll to see the entireassembly code for thisfunction, as shown below:
Viewing Type Information for a Structure
In WinDbg, execute this command: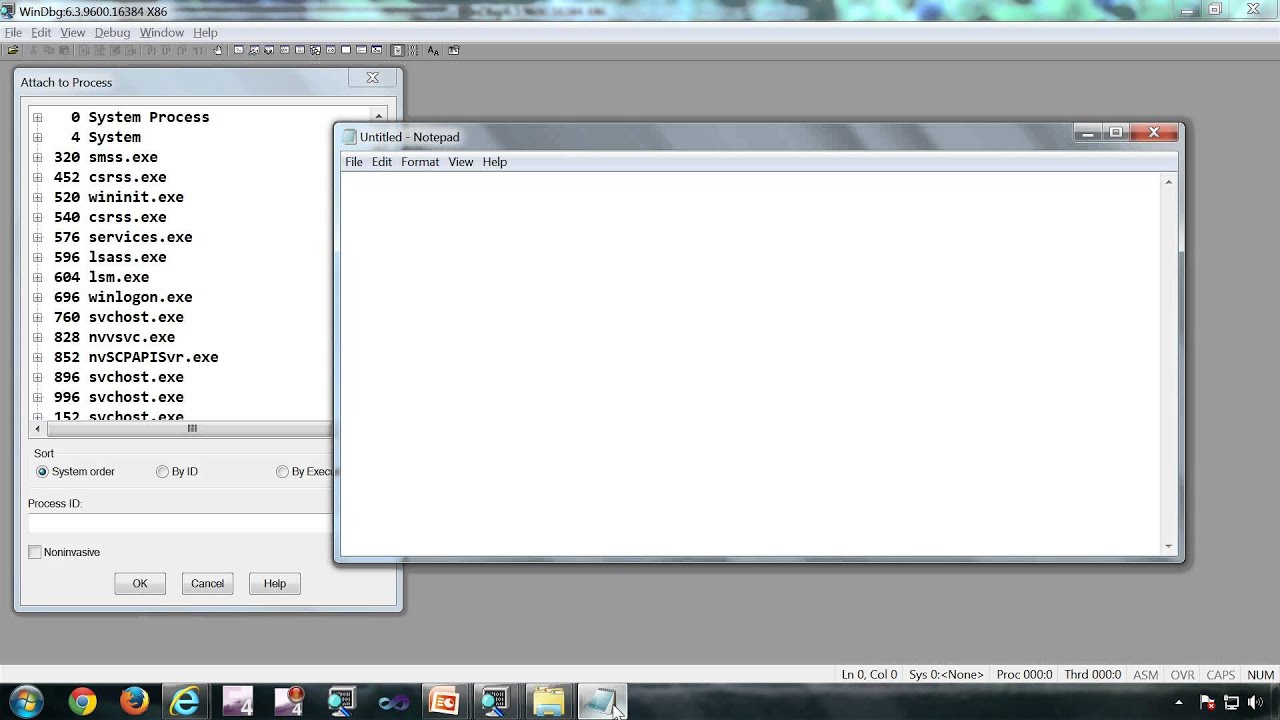
This shows the first few bytes of thefunction, disassembled,as shown below:
To see more of this function,it helps to use theWinDbg Disassembly window.
If the Command window is maximized,make it smaller.
From the WinDbg menu bar, clickView, Disassembly,as shown below:
In the Offset bar at the top,enter
nt!NtCreateFile
This shows the assembly code beforeand after the start of the NtCreateFilefunction. Using the up-arrowand down-arrow keys, you canscroll to see the entireassembly code for thisfunction, as shown below:
Viewing Type Information for a Structure
In WinDbg, execute this command:dt nt!_DRIVER_OBJECT
This shows the first few lines ofa driver object structure, whichstores information about a kerneldriver,as shown below. Notice the DriverStartpointer--this contains the location of thedriver in memory.
Challenge 15a: Function Name (5 pts)Find the Windows kernel function thathas a name fitting this pattern:two characters, RegistryKey,then six more letters, like this: |
Challenge 15b: Beep (10 pts)Disassemble the Beep module,near its DriverEntry.Find thehexadecimal valuescovered by the green boxin the image below. Use the formbelow toget your points.
|
References
Common WinDbg Commands (Thematically Grouped)!process
Posted 7-16-17 by Sam Bowne
Modified 7-26-17 2:10 pm
Hints for Beep added 10-23-18
-->
Symbol problems can show up in a variety of ways. Perhaps a stack trace shows incorrect information or fails to identify the names of the functions in the stack. Or perhaps a debugger command failed to understand the name of a module, function, variable, structure, or data type.
If you suspect that the debugger is not loading symbols correctly, there are several steps you can take to investigate this problem.
First, use the lm (List Loaded Modules) command to display the list of loaded modules with symbol information. The most useful form of this command is the following:
If you are using WinDbg, the Debug | Modules menu command will let you see this information as well.
Pay particular attention to any notes or abbreviations you may see in these displays. For an interpretation of these, see Symbol Status Abbreviations.
If you don't see the proper symbol files, the first thing to do is to check the symbol path: Trainz 2009 free download pc.
If your symbol path is wrong, fix it. If you are using the kernel debugger make sure your local %WINDIR% is not on your symbol path.
Then reload symbols using the .reload (Reload Module) command:
If your symbol path is correct, you should activate noisy mode so you can see which symbol files dbghelp is loading. Then reload your module. See Setting Symbol Options for information about how to activate noisy mode.
Here is an example of a 'noisy' reload of the Microsoft Windows symbols:
The symbol handler first looks for an image that matches the module it is trying to load (lines three and four). The image itself is not always necessary, but if an incorrect one is present, the symbol handler will often fail. These lines show that the debugger found an image at D:MyInstallationi386ntkrnlmp.exe, but the time-date stamp didn't match. Because the time-date stamp didn't match, the search continues. Next, the debugger looks for a .dbg file and a .pdb file that match the loaded image. These are on lines 6 through 10. Line 11 indicates that even though symbols were loaded, the time-date stamp for the image did not match (that is, the symbols were wrong).
If the symbol-search encountered a catastrophic failure, you would see a message of the form:
This could be caused by items such as file system failures, network errors, and corrupt .dbg files.
Diagnosing Symbol Loading Errors
When in noisy mode, the debugger may print out error codes when it cannot load a symbol file. The error codes for .dbg files are listed in winerror.h. The .pdb error codes come from another source and the most common errors are printed in plain English text.
Some common error codes for .dbg files from winerror.h are:
0xB
ERROR_BAD_FORMAT
0x3
ERROR_PATH_NOT_FOUND
0x35
ERROR_BAD_NETPATH
It's possible that the symbol file cannot be loaded because of a networking error. If you see ERROR_BAD_FORMAT or ERROR_BAD_NETPATH and you are loading symbols from another machine on the network, try copying the symbol file to your host computer and put its path in your symbol path. Then try to reload the symbols.
Verifying Your Search Path and Symbols
Let 'c:MyDir;c:SomeDir' represent your symbol path. Where should you look for debug information?
In cases where the binary has been stripped of debug information, such as the free builds of Windows, first look for a .dbg file in the following locations:
Next, look for a .pdb file in the following locations:
Note that in the search for the .dbg file, the debugger interleaves searching through the MyDir and SomeDir directories, but in the .pdb search it does not.
Windows XP and later versions of Windows do not use any .dbg symbol files. See Symbols and Symbol Files for details.
Mismatched Builds
One of the most common problems in debugging failures on a machine that is often updated is mismatched symbols from different builds. Three common causes of this problem are: pointing at symbols for the wrong build, using a privately built binary without the corresponding symbols, and using the uniprocessor hardware abstraction level (HAL) and kernel symbols on a multiprocessor machine. The first two are simply a matter of matching your binaries and symbols; the third can be corrected by renaming your hal*.dbg and ntkrnlmp.dbg to hal.dbg and ntoskrnl.dbg.
To find out what build of Windows is installed on the target computer, use the vertarget (Show Target Computer Version) command:
Testing the Symbols
Testing the symbols is more difficult. It involves verifying a stack trace on the debugger and seeing if the debug output is correct. Here's one example to try:
The u command unassembles the videoportfindadapter string in videoprt.sys. The symbols are correct on the debugger because common stack commands like push and mov show up on the stack. Most functions begin with an add, sub, or push operation using either the base pointer (ebp) or the stack pointer (esp).
It's usually obvious when the symbols aren't working correctly. Glintmp.sys doesn't have symbols in this example because a function isn't listed next to Glintmp:
The wrong build symbols were loaded for this stack trace. Notice how there are no functions listed for the first two calls. This stack trace looks like a problem with win32k.sys drawing rectangles:
Here's the correct stack trace. The problem is really with AGP440.sys. The first item appearing on a stack trace is usually at fault. Notice that the win32k.sys rectangle error is gone:
Useful Commands and Extensions
The following commands and extensions may be useful in tracking down symbol problems:
lm (List Loaded Modules)
Lists all modules and gives the loading status of all symbols in these modules.
!dh image-header-base
Displays header information for a loaded image beginning at image-header-base.
.reload /n
Reloads all kernel symbols.
.reload [image-name]
(CDB or WinDbg only) Reloads symbols for the image image-name. If no image-name is specified, reloads symbols for all images. (It is necessary to reload symbols after the symbol path has been changed.)
!sym noisy
Turns on verbose mode for symbol loads. This can be used to get information about the module loads. See Setting Symbol Options for details.
.sympath [new-symbol-path]
Sets a new symbol path, or displays the current symbol path. See Symbol Path for details.
If the kernel symbols are correct, but you aren't getting a complete stack, the following commands may also be useful:
X *!
This will list the modules which currently have symbols loaded. This is useful if the kernel symbols are correct. Repair manual downloads.
.reload /user
This will attempt to reload all user-mode symbols. This is needed while performing kernel debugging if symbols were loaded while one process was running, and a break later occurred in another process. In this case, the user-mode symbols from the new process will not be loaded unless this command is executed.
X wdmaud!*start*
This will list only the symbols in the wdmaud module whose names contain the 'start' string. This has the advantage that it forces the reloading of all the symbols in wdmaud, but only displays those with 'start' in them. (This means a shorter listing, but since there are always some symbols with 'start' in them, there will be some verification that the load has taken place.)
One other useful technique for verifying symbols is unassembling code. Most functions begin with an add, sub, or push operation using either the base pointer (ebp) or the stack pointer (esp or sp). Try unassembling (U Function) some of the functions on the stack (from offset zero) to verify the symbols.
Network and Port Problems
Problems will occur with the symbol files and while connecting to the debugger. Here are a few things to keep in mind if you encounter problems:
Livekd Could Not Resolve Symbols For Ntoskrnl.exe 7
Determine which COM port the debug cable is connected to on the test system.
Check the boot.ini settings of the test system. Look for the /debug switch and check the baud rate and COM port settings.
Network problems can interfere with debugging if the symbols files are accessed through the network.
.dll and .sys files with the same name (for example − mga64.sys and mga64.dll) will confuse the debugger if they aren't separated into the proper directories of the symbol tree.
The kernel debugger doesn't always like replacing the build symbol files with private symbol files. Double check the symbol path and do a .reloadFileName on the misbehaving symbol. The !dlls command is sometimes useful.
Questions and Misconceptions
Q: I've successfully loaded symbols, but the stack seems to be wrong. Is the debugger broken?
A: Not necessarily. The most likely cause of your problem is that you've got incorrect symbols. Go through the steps outlined in this section to determine whether you've loaded valid symbols or not. Do not assume that because some things work you have valid symbols. For example, you very well may be able to execute dd nt!ntbuildnumber or u nt!KeInitializeProcess with incorrect symbols. Verify that they are correct using the procedures outlined above.
Q: Will the debugger still work with incorrect symbols?
A: Yes and no. Often you can get away with symbols that don't strictly match. For example, symbols from a previous Windows build will often work in certain cases, but there is no rule as to when this will work and when it will not.
Q: I'm stopped in the kernel debugger and I want to view symbols for my user-mode process. Can I do it?
A: Mostly. The support for this scenario is poor because the kernel debugger doesn't keep enough information around to track the module loads for each process, but there's a reasonable workaround. To load symbols for a user-mode module, execute a .reload -user command. This will load the user-mode modules for the current context.
Q: What does the following message mean?
*** WARNING: symbols checksum and timestamp is wrong 0x0036d6bf 0x0036ab55 for ntkrnlmp.exe
Livekd Could Not Resolve Symbols For Ntoskrnl.exe 11
A: It means your symbols for ntkrnlmp.exe are wrong.
